Penetration
Testing


Hire the Good Guys.
Infinite Threat. Finite Budget.
One Solution.
What is the most valuable asset to any attacker? Time. At Secure Yeti, we know yours is finite. By blending programmatic speed with deep manual expertise, we compress a year’s worth of adversary persistence into a single, budget-conscious engagement. High-impact security that respects your ROI.
As a leading penetration testing company, we offer ethical hacking services that are anything but mythical. We find the gaps in your armor and give you a clear, actionable map to fix them.
Who Needs It
Organizations that have outgrown “check-the-box” security and require a rigorous, human-led defense to protect their most critical assets. Whether you’re safeguarding sensitive data or hardening a complex infrastructure, we provide the clarity needed to stay one step ahead of the breach.

Offensive Strategy
The Yeti Edge
Actionable Results
Beyond the Breach

What We Provide
Stop guessing and start knowing with a custom penetration test that reveals your true security posture. Validate your defenses today and get the actionable roadmap you need to eliminate the threat, starting with a brief consultation:

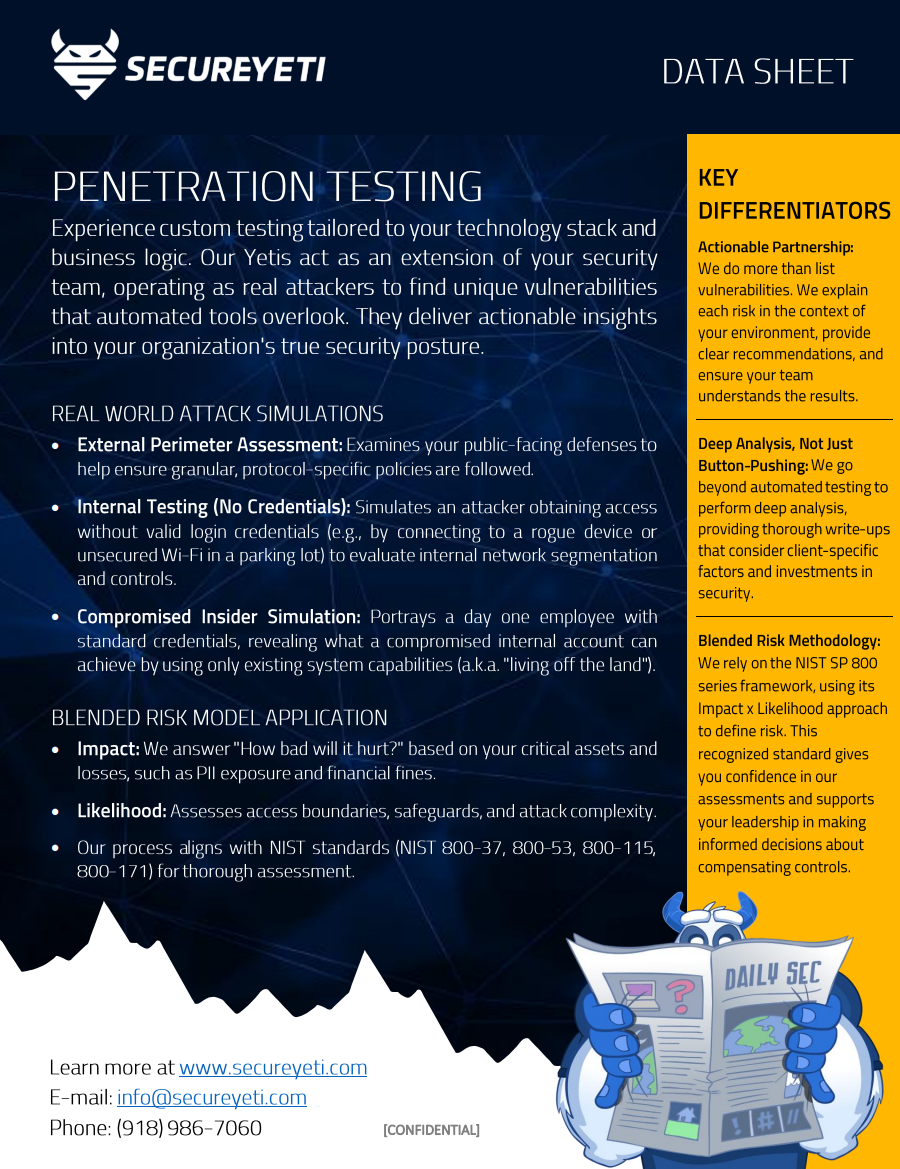
Create Teaching Moments
Discover how we encourage and empower your employees to harness their natural situational awareness to better protect themselves and the company. Download our Penetration Testing Data Sheet.

