Security
Architecture


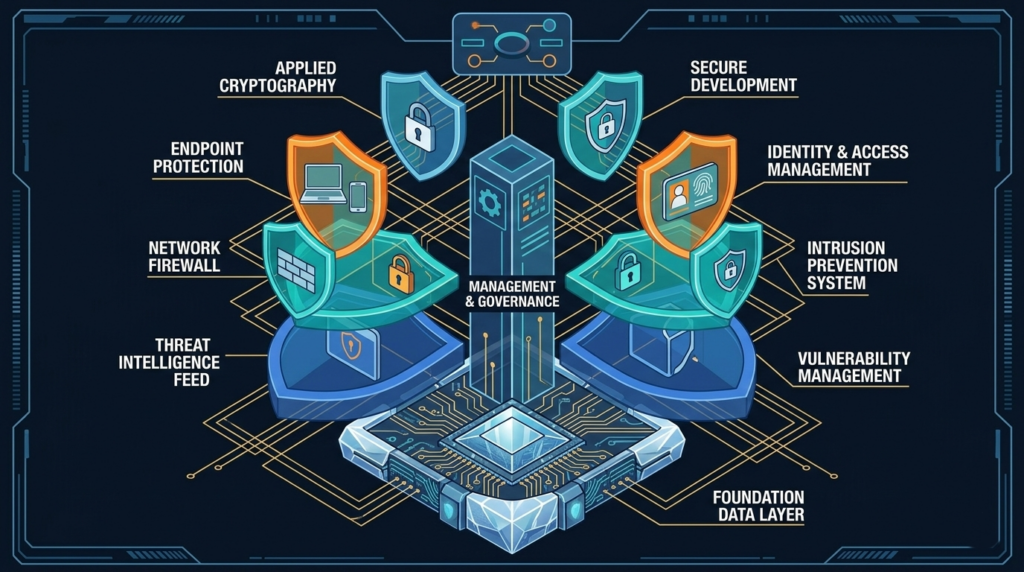
Protection by Design
Security doesn’t happen by accident. Having a security architecture means you have a plan to apply security controls to protect your data and your business. Work with our Yetis to assess and strengthen your risk posture.
Who Needs It
Every company takes action to protect its sensitive data and critical applications from threats and breaches. The more complex the organization, the more likely it is that new technologies and policies have created conflicts or unseen gaps.
It’s critically important to ensure these actions, including policies, procedures, and tools, are all aligned to your key business objectives. That’s the purpose of a security architecture, to create a strong foundation for your collective security and compliance activities.
Let us help you develop or mature your security architecture.

Gap and Risk Assessment
Device Inventory and Network Access Control

What We Provide

Compliance Built
into Every Service





Talk to a Trusted Advisor

